In Part 1 of this series we covered what blacklists are and the different types available. Here we'll look at how administrators use them to control inbound spam.
How Are They Used?
Most mail server software can query DNSBLs during message processing, then accept or reject mail based on whether the sending IP appears on a list. For URIBLs, the check runs against domain names found in the message body rather than the sender's IP.
Example: Exim
The Exim MTA supports specifying one or more DNSBLs during ACL processing of an inbound SMTP message.
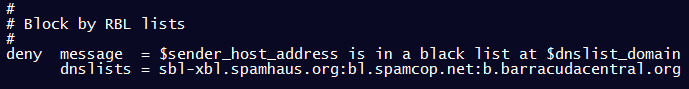
Exim performs a DNS lookup on the sending server's IP address. If it appears in a configured DNSBL, Exim rejects the message with a specific error response.
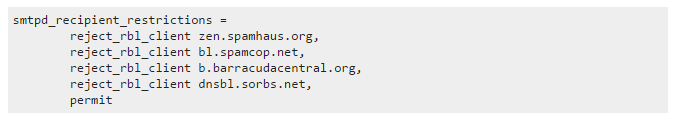
Example: Postfix
The Postfix MTA lets administrators add DNSBLs via the reject_rbl_client option in smtpd_recipient_restrictions.
If you're configuring either of these MTAs, GoodTLS has production-ready TLS cipher suite recommendations for both Exim and Postfix.
Manual Lookup
You can also run a quick check from any command line using nslookup. Reverse the octets of the IP address and append the DNSBL hostname. To check 127.0.0.2 against SpamCop's bl.spamcop.net:
nslookup 2.0.0.127.bl.spamcop.net
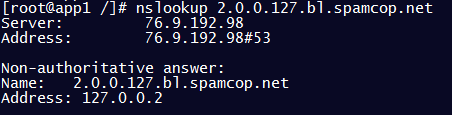
Manual lookups work for spot checks, but they don't scale. Automated RBL monitoring covers your full address space across hundreds of blacklists, alerting you the moment something appears.
In Part 3 we cover how blacklisting affects your organization and why staying on top of your listing status matters.